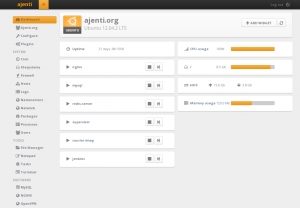
Ajenti ist ein webbasiertes in Python geschriebenes Admin-Panel für Linux und FreeBSD (experimentell) mit moderner, AJAX basierter Oberfläche. Die Version 1.0 wurde im August 2013 veröffentlicht. Es gibt viele Plugins welche die browserbasierte Konfiguration erlauben:
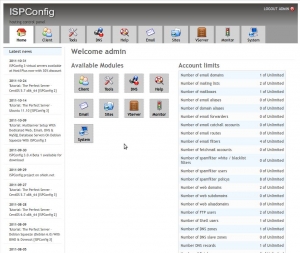
ISPConfig (Internet Service Provider Configuration) wurde von der Projektfarm GmbH unter Till Brehm und Falko Timme entwickelt und zunächst unter 42go.de als proprietäre Software vertrieben.
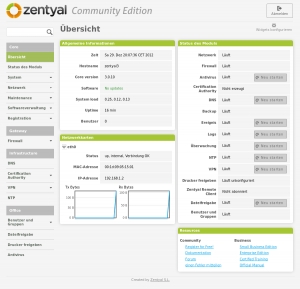
Zentyal ist eine in Spanien entwickelte grafische Oberfläche für die Server-Version von Ubuntu 12.04. Dadurch wird die oft mühsame und zeitraubende manuelle Installation und Konfiguration eines eigenen Servers erheblich vereinfacht.
Webmin (Kunstwort aus Web-Administration) ist ein freies Programmpaket zur Fernverwaltung eines Rechners mit einem Unix-artigen Betriebssystem. Es lauscht im Hintergrund auf Anfragen aus dem Internet oder dem lokalen Netz.
-
Red Hat Security Advisory 2024-1899-03
Operating System: RedHat ≈ Packet Storm Apr 26, 2024 | 15:08 pmRed Hat Security Advisory 2024-1899-03 - Red Hat OpenShift Container Platform release 4.12.56 is now available with updates to packages and images that fix several bugs and add enhancements. Issues addressed include a denial of service vulnerability.
Read more... -
Red Hat Security Advisory 2024-2062-03
Operating System: RedHat ≈ Packet Storm Apr 26, 2024 | 15:08 pmRed Hat Security Advisory 2024-2062-03 - An update is now available for Service Telemetry Framework 1.5.4 for RHEL 9. Issues addressed include a denial of service vulnerability.
Read more... -
Red Hat Security Advisory 2024-2063-03
Operating System: RedHat ≈ Packet Storm Apr 26, 2024 | 15:08 pmRed Hat Security Advisory 2024-2063-03 - An update for yajl is now available for Red Hat Enterprise Linux 8.6 Extended Update Support. Issues addressed include buffer overflow, integer overflow, and memory leak vulnerabilities.
Read more... -
Red Hat Security Advisory 2024-2064-03
Operating System: RedHat ≈ Packet Storm Apr 26, 2024 | 15:08 pmRed Hat Security Advisory 2024-2064-03 - An update for buildah is now available for Red Hat Enterprise Linux 9.2 Extended Update Support.
Read more... -
Red Hat Security Advisory 2024-2066-03
Operating System: RedHat ≈ Packet Storm Apr 26, 2024 | 15:08 pmRed Hat Security Advisory 2024-2066-03 - An update for buildah is now available for Red Hat Enterprise Linux 9.0 Extended Update Support.
Read more... -
Red Hat Security Advisory 2024-1887-03
Operating System: RedHat ≈ Packet Storm Apr 26, 2024 | 15:07 pmRed Hat Security Advisory 2024-1887-03 - Red Hat OpenShift Container Platform release 4.15.10 is now available with updates to packages and images that fix several bugs and add enhancements. Issues addressed include a denial of service vulnerability.
Read more... -
Red Hat Security Advisory 2024-1892-03
Operating System: RedHat ≈ Packet Storm Apr 26, 2024 | 15:07 pmRed Hat Security Advisory 2024-1892-03 - Red Hat OpenShift Container Platform release 4.15.10 is now available with updates to packages and images that fix several bugs and add enhancements. Issues addressed include a denial of service vulnerability.
Read more... -
Red Hat Security Advisory 2024-1896-03
Operating System: RedHat ≈ Packet Storm Apr 26, 2024 | 15:07 pmRed Hat Security Advisory 2024-1896-03 - Red Hat OpenShift Container Platform release 4.12.56 is now available with updates to packages and images that fix several bugs and add enhancements. Issues addressed include denial of service and traversal vulnerabilities.
Read more... -
Red Hat Security Advisory 2024-2055-03
Operating System: RedHat ≈ Packet Storm Apr 25, 2024 | 14:19 pmRed Hat Security Advisory 2024-2055-03 - An update for buildah is now available for Red Hat Enterprise Linux 9.
Read more... -
Red Hat Security Advisory 2024-2060-03
Operating System: RedHat ≈ Packet Storm Apr 25, 2024 | 14:19 pmRed Hat Security Advisory 2024-2060-03 - Red Hat OpenShift Virtualization release 4.14.5 is now available with updates to packages and images that fix several bugs and add enhancements. Issues addressed include a denial of service vulnerability.
Read more... -
The Product Security Blog has moved!
Red Hat Security Blog Blog Posts Mar 19, 2019 | 19:38 pmRed Hat Product Security has joined forces with other security teams inside Red Hat to publish our content in a common venue using the Security channel of the Red Hat Blog.This move provides a wider variety of important Security topics,[…]
Read more... -
New Red Hat Product Security OpenPGP key
Red Hat Security Blog Blog Posts Aug 22, 2018 | 13:30 pmRed Hat Product Security has transitioned from using its old 1024-bit DSA OpenPGP key to a new 4096-bit RSA OpenPGP key.This was done to improve the long-term security of our communications with our customers and also to meet current key[…]
Read more... -
SPECTRE Variant 1 scanning tool
Red Hat Security Blog Blog Posts Jul 18, 2018 | 13:30 pmAs part of Red Hat's commitment to product security we have developed a tool internally that can be used to scan for variant 1 SPECTRE vulnerabilities. As part of our commitment to the wider user community, we are introducing this[…]
Read more... -
Red Hat’s disclosure process
Red Hat Security Blog Blog Posts Jul 10, 2018 | 13:00 pmLast week, a vulnerability (CVE-2018-10892) that affected CRI-O, Buildah, Podman, and Docker was made public before some affected upstream projects were notified. We regret that this was not handled in a way that lives up to our own standards around[…]
Read more... -
Join us in San Francisco at the 2018 Red Hat Summit
Red Hat Security Blog Blog Posts Apr 23, 2018 | 14:30 pmThis year’s Red Hat Summit will be held on May 8-10 in beautiful San Francisco, USA.Product Security will be joining many Red Hat security experts in presenting and assisting subscribers and partners at the show.Here is a sneak peek at[…]
Read more... -
Certificate Transparency and HTTPS
Red Hat Security Blog Blog Posts Apr 17, 2018 | 15:00 pmGoogle has announced that on April 30, 2018, Chrome will:“...require that all TLS server certificates issued after 30 April, 2018 be compliant with the Chromium CT Policy. After this date, when Chrome connects to a site serving a publicly-trusted certificate[…]
Read more... -
Let's talk about PCI-DSS
Red Hat Security Blog Blog Posts Feb 28, 2018 | 14:30 pmFor those who aren’t familiar with Payment Card Industry Data Security Standard (PCI-DSS), it is the standard that is intended to protect our credit card data as it flows between systems and is stored in company databases.PCI-DSS requires that all[…]
Read more... -
Security is from Mars, Developers are from Venus…...or ARE they?
Red Hat Security Blog Blog Posts Nov 16, 2017 | 15:00 pmIt is a tale as old as time.Developers and security personnel view each other withsuspicion.The perception is that a vast gulf of understanding and ability lies between the two camps.“They can’t possibly understand what it is to do my job!”[…]
Read more... -
Abuse of RESTEasy Default Providers in JBoss EAP
Red Hat Security Blog Blog Posts Oct 18, 2017 | 13:30 pmRed Hat JBoss Enterprise Application Platform (EAP) is a commonly used host for Restful webservices. A powerful but potentially dangerous feature of Restful webservices on JBoss EAP is the ability to accept any media type. If not configured to accept[…]
Read more... -
Kernel Stack Protector and BlueBorne
Red Hat Security Blog Blog Posts Sep 12, 2017 | 11:51 amToday, a security issue called BlueBorne was disclosed, a vulnerability that could be used to attack sensitive systems via the Bluetooth protocol. Specifically, BlueBorne is a flaw where a remote (but physically quite close) attacker could get root on a[…]
Read more...
-
Debian Security Advisory 5674-1
Operating System: Debian ≈ Packet Storm Apr 26, 2024 | 15:13 pmDebian Linux Security Advisory 5674-1 - It was discovered that PDNS Recursor, a resolving name server, was susceptible to denial of service if recursive forwarding is configured.
Read more... -
Debian Security Advisory 5673-1
Operating System: Debian ≈ Packet Storm Apr 23, 2024 | 16:10 pmDebian Linux Security Advisory 5673-1 - Charles Fol discovered that the iconv() function in the GNU C library is prone to a buffer overflow vulnerability when converting strings to the ISO-2022-CN-EXT character set, which may lead to denial of service[…]
Read more... -
Debian Security Advisory 5672-1
Operating System: Debian ≈ Packet Storm Apr 23, 2024 | 15:59 pmDebian Linux Security Advisory 5672-1 - Several vulnerabilities have been discovered in the OpenJDK Java runtime, which may result in denial of service or information disclosure.
Read more... -
Debian Security Advisory 5671-1
Operating System: Debian ≈ Packet Storm Apr 23, 2024 | 15:51 pmDebian Linux Security Advisory 5671-1 - Several vulnerabilities have been discovered in the OpenJDK Java runtime, which may result in denial of service or information disclosure.
Read more... -
Debian Security Advisory 5670-1
Operating System: Debian ≈ Packet Storm Apr 23, 2024 | 15:48 pmDebian Linux Security Advisory 5670-1 - Multiple security issues were discovered in Thunderbird, which could result in denial of service or the execution of arbitrary code.
Read more... -
Debian Security Advisory 5667-1
Operating System: Debian ≈ Packet Storm Apr 22, 2024 | 16:22 pmDebian Linux Security Advisory 5667-1 - Several security vulnerabilities have been discovered in the Tomcat servlet and JSP engine.
Read more... -
Debian Security Advisory 5668-1
Operating System: Debian ≈ Packet Storm Apr 22, 2024 | 12:11 pmDebian Linux Security Advisory 5668-1 - Security issues were discovered in Chromium, which could result in the execution of arbitrary code, denial of service or information disclosure.
Read more... -
Debian Security Advisory 5666-1
Operating System: Debian ≈ Packet Storm Apr 22, 2024 | 12:11 pmDebian Linux Security Advisory 5666-1 - Gergo Koteles discovered that sandbox restrictions in Flatpak, an application deployment framework for desktop apps, could by bypassed in combination with xdg-desktop-portal.
Read more... -
Debian Security Advisory 5669-1
Operating System: Debian ≈ Packet Storm Apr 22, 2024 | 11:30 amDebian Linux Security Advisory 5669-1 - It was discovered that insufficient restriction of unix daemon sockets in the GNU Guix functional package manager could result in sandbox bypass.
Read more... -
Debian Security Advisory 5665-1
Operating System: Debian ≈ Packet Storm Apr 18, 2024 | 15:54 pmDebian Linux Security Advisory 5665-1 - Several security vulnerabilities have been discovered in the Tomcat servlet and JSP engine.
Read more...
-
Ubuntu Security Notice USN-6753-1
Operating System: Ubuntu ≈ Packet Storm Apr 26, 2024 | 15:13 pmUbuntu Security Notice 6753-1 - Thomas Neil James Shadwell discovered that CryptoJS was using an insecure cryptographic default configuration. A remote attacker could possibly use this issue to expose sensitive information.
Read more... -
Ubuntu Security Notice USN-6754-1
Operating System: Ubuntu ≈ Packet Storm Apr 26, 2024 | 15:13 pmUbuntu Security Notice 6754-1 - It was discovered that nghttp2 incorrectly handled the HTTP/2 implementation. A remote attacker could possibly use this issue to cause nghttp2 to consume resources, leading to a denial of service. This issue only affected Ubuntu[…]
Read more... -
Ubuntu Security Notice USN-6752-1
Operating System: Ubuntu ≈ Packet Storm Apr 26, 2024 | 15:12 pmUbuntu Security Notice 6752-1 - It was discovered that FreeRDP incorrectly handled certain memory operations. If a user were tricked into connecting to a malicious server, a remote attacker could possibly use this issue to cause FreeRDP to crash, resulting[…]
Read more... -
Ubuntu Security Notice USN-6751-1
Operating System: Ubuntu ≈ Packet Storm Apr 26, 2024 | 15:12 pmUbuntu Security Notice 6751-1 - It was discovered that Zabbix incorrectly handled input data in the discovery and graphs pages. A remote authenticated attacker could possibly use this issue to perform reflected cross-site scripting attacks.
Read more... -
Ubuntu Security Notice USN-6750-1
Operating System: Ubuntu ≈ Packet Storm Apr 25, 2024 | 14:28 pmUbuntu Security Notice 6750-1 - Multiple security issues were discovered in Thunderbird. If a user were tricked into opening a specially crafted website in a browsing context, an attacker could potentially exploit these to cause a denial of service, obtain[…]
Read more... -
Ubuntu Security Notice USN-6743-3
Operating System: Ubuntu ≈ Packet Storm Apr 25, 2024 | 14:27 pmUbuntu Security Notice 6743-3 - Several security issues were discovered in the Linux kernel. An attacker could possibly use these to compromise the system.
Read more... -
Ubuntu Security Notice USN-6657-2
Operating System: Ubuntu ≈ Packet Storm Apr 25, 2024 | 14:26 pmUbuntu Security Notice 6657-2 - USN-6657-1 fixed several vulnerabilities in Dnsmasq. This update provides the corresponding update for Ubuntu 16.04 LTS and Ubuntu 18.04 LTS. Elias Heftrig, Haya Schulmann, Niklas Vogel, and Michael Waidner discovered that Dnsmasq incorrectly handled validating[…]
Read more... -
Ubuntu Security Notice USN-6749-1
Operating System: Ubuntu ≈ Packet Storm Apr 25, 2024 | 14:25 pmUbuntu Security Notice 6749-1 - It was discovered that FreeRDP incorrectly handled certain context resets. If a user were tricked into connecting to a malicious server, a remote attacker could use this issue to cause FreeRDP to crash, resulting in[…]
Read more... -
Ubuntu Security Notice USN-6747-1
Operating System: Ubuntu ≈ Packet Storm Apr 24, 2024 | 15:20 pmUbuntu Security Notice 6747-1 - Multiple security issues were discovered in Firefox. If a user were tricked into opening a specially crafted website, an attacker could potentially exploit these to cause a denial of service, obtain sensitive information across domains,[…]
Read more... -
Ubuntu Security Notice USN-6748-1
Operating System: Ubuntu ≈ Packet Storm Apr 24, 2024 | 15:20 pmUbuntu Security Notice 6748-1 - It was discovered that Sanitize incorrectly handled noscript elements under certain circumstances. An attacker could possibly use this issue to execute a cross-site scripting attack. This issue only affected Ubuntu 22.04 LTS. It was discovered[…]
Read more...
-
chromium -- multiple security fixes
FreeBSD VuXML Apr 25, 2024 | 00:00 am
Read more... -
py-matrix-synapse -- weakness in auth chain indexing allows DoS
FreeBSD VuXML Apr 24, 2024 | 00:00 am
Read more... -
Gitlab -- vulnerabilities
FreeBSD VuXML Apr 24, 2024 | 00:00 am
Read more... -
ruby -- Arbitrary memory address read vulnerability with Regex search
FreeBSD VuXML Apr 23, 2024 | 00:00 am
Read more... -
sdl2_sound -- multiple vulnerabilities
FreeBSD VuXML Apr 22, 2024 | 00:00 am
Read more... -
GLPI -- multiple vulnerabilities
FreeBSD VuXML Apr 22, 2024 | 00:00 am
Read more... -
GLPI -- multiple vulnerabilities
FreeBSD VuXML Apr 22, 2024 | 00:00 am
Read more... -
GLPI -- multiple vulnerabilities
FreeBSD VuXML Apr 22, 2024 | 00:00 am
Read more... -
chromium -- multiple security fixes
FreeBSD VuXML Apr 21, 2024 | 00:00 am
Read more...
-
Glibc Tunables Privilege Escalation
Operating System: Fedora ≈ Packet Storm Dec 21, 2023 | 14:20 pmA buffer overflow exists in the GNU C Library's dynamic loader ld.so while processing the GLIBC_TUNABLES environment variable. It has been dubbed Looney Tunables. This issue allows an local attacker to use maliciously crafted GLIBC_TUNABLES when launching binaries with SUID[…]
Read more... -
GNOME Files 43.4 Privilege Escalation
Operating System: Fedora ≈ Packet Storm Aug 8, 2023 | 15:54 pmGNOME Files version 43.4 (nautilus) on Fedora 37 will extract zip archives with setuid files for other user identifiers that can be leveraged to escalate privileges.
Read more... -
Apache Tomcat Privilege Escalation
Operating System: Fedora ≈ Packet Storm Mar 14, 2023 | 14:39 pmThis Metasploit module exploits a vulnerability in RedHat based systems where improper file permissions are applied to /usr/lib/tmpfiles.d/tomcat.conf for Apache Tomcat versions before 7.0.54-8. The configuration files in tmpfiles.d are used by systemd-tmpfiles to manage temporary files including their creation.[…]
Read more... -
Sequoia: A Deep Root In Linux's Filesystem Layer
Operating System: Fedora ≈ Packet Storm Jul 21, 2021 | 16:10 pmQualys discovered a size_t-to-int conversion vulnerability in the Linux kernel's filesystem layer: by creating, mounting, and deleting a deep directory structure whose total path length exceeds 1GB, an unprivileged local attacker can write the 10-byte string "//deleted" to an offset[…]
Read more... -
Fedora / Gnome fscaps Issue
Operating System: Fedora ≈ Packet Storm Jun 22, 2021 | 19:20 pmFedora with Gnome has an issue where it is not using fscaps safely.
Read more... -
netkit-telnet 0.17 Remote Code Execution
Operating System: Fedora ≈ Packet Storm Mar 5, 2020 | 20:57 pmnetkit-telnet version 0.17 telnetd on Fedora 31 BraveStarr remote code execution exploit.
Read more... -
vReliable Datagram Sockets (RDS) rds_page_copy_user Privilege Escalation
Operating System: Fedora ≈ Packet Storm Dec 23, 2019 | 21:02 pmThis Metasploit module exploits a vulnerability in the rds_page_copy_user function in net/rds/page.c (RDS) in Linux kernel versions 2.6.30 to 2.6.36-rc8 to execute code as root (CVE-2010-3904). This module has been tested successfully on Fedora 13 (i686) kernel version 2.6.33.3-85.fc13.i686.PAE and[…]
Read more... -
Grub2 grub2-set-bootflag Environment Corruption
Operating System: Fedora ≈ Packet Storm Nov 27, 2019 | 23:02 pmGrub2 has grub2-set-bootflag setuid in the new Fedora release and has the ability to corrupt the environment.
Read more... -
SystemTap 1.3 MODPROBE_OPTIONS Privilege Escalation
Operating System: Fedora ≈ Packet Storm Apr 19, 2019 | 13:28 pmThis Metasploit module attempts to gain root privileges by exploiting a vulnerability in the staprun executable included with SystemTap version 1.3. The staprun executable does not clear environment variables prior to executing modprobe, allowing an arbitrary configuration file to be[…]
Read more... -
Linux Nested User Namespace idmap Limit Local Privilege Escalation
Operating System: Fedora ≈ Packet Storm Nov 28, 2018 | 01:51 amThis Metasploit module exploits a vulnerability in Linux kernels 4.15.0 to 4.18.18, and 4.19.0 to 4.19.1, where broken uid/gid mappings between nested user namespaces and kernel uid/gid mappings allow elevation to root (CVE-2018-18955). The target system must have unprivileged user[…]
Read more...