Service (16)
Unterkategorien
Security News (14)

Im Sinne der Aktualität sind diese News grösstenteils in englischer Sprache. Falls nötig, bitte die Übersetzungsfunktion verwenden.
Artikel anzeigen...Workshops (2)

Installationen, Konfigurationen mit Bildern und Videos verständlich erklärt
Artikel anzeigen...-
Ruby-SAML / GitLab Authentication Bypass
Ruby Files ≈ Packet Storm Oct 7, 2024 | 14:14 pmThis script exploits the issue noted in CVE-2024-45409 that allows an unauthenticated attacker with access to any signed SAML document issued by the IDP to forge a SAML Response/Assertion and gain access as any user on GitLab. Ruby-SAML versions below[…]
Read more... -
Debian Security Advisory 5774-1
Ruby Files ≈ Packet Storm Sep 23, 2024 | 14:43 pmDebian Linux Security Advisory 5774-1 - It was discovered that ruby-saml, a SAML library implementing the client side of a SAML authorization, does not properly verify the signature of the SAML Response, which could result in bypass of authentication in[…]
Read more... -
Red Hat Security Advisory 2024-6784-03
Ruby Files ≈ Packet Storm Sep 19, 2024 | 13:39 pmRed Hat Security Advisory 2024-6784-03 - An update for the ruby:3.3 module is now available for Red Hat Enterprise Linux 8. Issues addressed include a denial of service vulnerability.
Read more... -
Red Hat Security Advisory 2024-6785-03
Ruby Files ≈ Packet Storm Sep 19, 2024 | 13:39 pmRed Hat Security Advisory 2024-6785-03 - An update for the ruby:3.3 module is now available for Red Hat Enterprise Linux 9. Issues addressed include a denial of service vulnerability.
Read more... -
Ruby On Rails JSON Processor YAML Deserialization Scanner
Ruby Files ≈ Packet Storm Sep 1, 2024 | 17:10 pmThis Metasploit module attempts to identify Ruby on Rails instances vulnerable to an arbitrary object instantiation flaw in the JSON request processor.
Read more... -
Ruby On Rails XML Processor YAML Deserialization Scanner
Ruby Files ≈ Packet Storm Sep 1, 2024 | 16:04 pmThis Metasploit module attempts to identify Ruby on Rails instances vulnerable to an arbitrary object instantiation flaw in the XML request processor.
Read more... -
Ruby On Rails Devise Authentication Password Reset
Ruby Files ≈ Packet Storm Aug 31, 2024 | 21:43 pmThe Devise authentication gem for Ruby on Rails is vulnerable to a password reset exploit leveraging type confusion. By submitting XML to rails, we can influence the type used for the reset_password_token parameter. This allows for resetting passwords of arbitrary[…]
Read more... -
Apple TV Video Remote Control
Ruby Files ≈ Packet Storm Aug 31, 2024 | 21:27 pmThis Metasploit module plays a video on an AppleTV device. Note that AppleTV can be somewhat picky about the server that hosts the video. Tested servers include default IIS, default Apache, and Rubys WEBrick. For WEBrick, the default MIME list[…]
Read more... -
Ruby On Rails File Content Disclosure
Ruby Files ≈ Packet Storm Aug 31, 2024 | 19:37 pmThis Metasploit module uses a path traversal vulnerability in Ruby on Rails versions 5.2.2 and below to read files on a target server.
Read more... -
Nuuo Central Management Server Authenticated Arbitrary File Download
Ruby Files ≈ Packet Storm Aug 31, 2024 | 18:49 pmThe Nuuo Central Management Server allows an authenticated user to download files from the installation folder. This functionality can be abused to obtain administrative credentials, the SQL Server database password and arbitrary files off the system with directory traversal. The[…]
Read more...
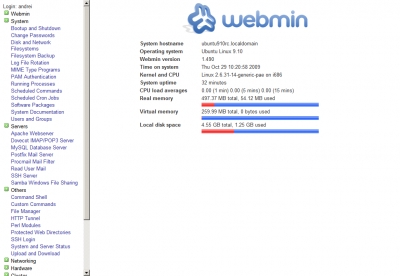
Diese Module beschreiben alles, was mit der Administration des Grundsystems verbunden ist. Dazu gehören zum Beispiel Startverhalten, Anwenderverwaltung, Software-Installation und derzeit laufende Prozesse.
Vorbereitung und Installation
Um Webmin auf Ihrem System laufen zu lassen, benötigen Sie einige Pakete, die eventuell in der Standardinstallation Ihrer Distribution nicht vorhanden sind. Mittels yum, apt und Konsorten ist es aber ein Leichtes, diese Packages nachzuziehen. Vor allen Dingen lösen yum und apt die Abhängigkeiten von selbst auf und installieren selbstständig alles Notwendige.
-
Grafana Remote Code Execution
Python Files ≈ Packet Storm Oct 24, 2024 | 13:37 pmThis repository contains a Python script that exploits a remote code execution vulnerability in Grafana's SQL Expressions feature. By leveraging insufficient input sanitization, this exploit allows an attacker to execute arbitrary shell commands on the server. This is made possible[…]
Read more... -
Red Hat Security Advisory 2024-8365-03
Python Files ≈ Packet Storm Oct 24, 2024 | 13:23 pmRed Hat Security Advisory 2024-8365-03 - An update for python-idna is now available for Red Hat Enterprise Linux 7 Extended Lifecycle Support. Issues addressed include a denial of service vulnerability.
Read more... -
Debian Security Advisory 5795-1
Python Files ≈ Packet Storm Oct 22, 2024 | 15:51 pmDebian Linux Security Advisory 5795-1 - Cedric Krier discovered that python-sql, a library to write SQL queries in a pythonic way, performed insufficient sanitizing which could result in SQL injection.
Read more... -
Red Hat Security Advisory 2024-8102-03
Python Files ≈ Packet Storm Oct 15, 2024 | 14:04 pmRed Hat Security Advisory 2024-8102-03 - An update for python-gevent is now available for Red Hat Enterprise Linux 8.8 Extended Update Support. Issues addressed include a privilege escalation vulnerability.
Read more... -
Red Hat Security Advisory 2024-8105-03
Python Files ≈ Packet Storm Oct 15, 2024 | 14:04 pmRed Hat Security Advisory 2024-8105-03 - An update for python-gevent is now available for Red Hat Enterprise Linux 8.4 Advanced Mission Critical Update Support, Red Hat Enterprise Linux 8.4 Update Services for SAP Solutions, and Red Hat Enterprise Linux 8.4[…]
Read more... -
Ubuntu Security Notice USN-7015-4
Python Files ≈ Packet Storm Oct 14, 2024 | 13:44 pmUbuntu Security Notice 7015-4 - USN-7015-1 fixed several vulnerabilities in Python. This update provides the corresponding update for CVE-2023-27043 for python2.7 and python3.5 in Ubuntu 14.04 LTS. It was discovered that the Python email module incorrectly parsed email addresses that[…]
Read more... -
Debian Security Advisory 5791-1
Python Files ≈ Packet Storm Oct 14, 2024 | 13:43 pmDebian Linux Security Advisory 5791-1 - Elyas Damej discovered that a sandbox mechanism in ReportLab, a Python library to create PDF documents, could be bypassed which may result in the execution of arbitrary code when converting malformed HTML to a[…]
Read more... -
Red Hat Security Advisory 2024-7785-03
Python Files ≈ Packet Storm Oct 8, 2024 | 14:26 pmRed Hat Security Advisory 2024-7785-03 - An update for python-gevent is now available for Red Hat Enterprise Linux 8.2 Advanced Update Support. Issues addressed include a privilege escalation vulnerability.
Read more... -
Grav CMS 1.7.44 Server-Side Template Injection
Python Files ≈ Packet Storm Oct 7, 2024 | 14:22 pmGenGravSSTIExploit is a proof of concept Python script that exploits an authenticated server-side template injection (SSTI) vulnerability in Grav CMS versions 1.7.44 and below. This vulnerability allows a user with editor permissions to execute OS commands on a remote server.
Read more... -
Ubuntu Security Notice USN-7015-3
Python Files ≈ Packet Storm Oct 1, 2024 | 13:47 pmUbuntu Security Notice 7015-3 - USN-7015-1 fixed several vulnerabilities in Python. This update provides the corresponding updates for CVE-2023-27043 for python2.7 in Ubuntu 16.04 LTS, Ubuntu 18.04 LTS, Ubuntu 20.04 LTS, and Ubuntu 22.04 LTS, and for python3.5 in Ubuntu[…]
Read more...
-
Debian Security Advisory 5780-1
CGI Files ≈ Packet Storm Oct 3, 2024 | 13:50 pmDebian Linux Security Advisory 5780-1 - Multiple security issues were found in PHP, a widely-used open source general purpose scripting language which could result in incorrect parsing of multipart/form-data, bypass of the cgi.force_direct directive or incorrect logging.
Read more... -
Ubuntu Security Notice USN-7049-1
CGI Files ≈ Packet Storm Oct 2, 2024 | 13:55 pmUbuntu Security Notice 7049-1 - It was discovered that PHP incorrectly handled parsing multipart form data. A remote attacker could possibly use this issue to inject payloads and cause PHP to ignore legitimate data. It was discovered that PHP incorrectly[…]
Read more... -
Supermicro Onboard IPMI CGI Scanner
CGI Files ≈ Packet Storm Sep 1, 2024 | 16:45 pmThis Metasploit module checks for known vulnerabilities in the CGI applications of Supermicro Onboard IPMI controllers. These issues currently include several unauthenticated buffer overflows in the login.cgi and close_window.cgi components.
Read more... -
Zen Load Balancer Directory Traversal
CGI Files ≈ Packet Storm Sep 1, 2024 | 16:40 pmThis Metasploit module exploits a authenticated directory traversal vulnerability in Zen Load Balancer v3.10.1. The flaw exists in index.cgi not properly handling filelog= parameter which allows a malicious actor to load arbitrary file path.
Read more... -
DnaLIMS Directory Traversal
CGI Files ≈ Packet Storm Sep 1, 2024 | 16:34 pmThis Metasploit module exploits a directory traversal vulnerability found in dnaLIMS. Due to the way the viewAppletFsa.cgi script handles the secID parameter, it is possible to read a file outside the www directory.
Read more... -
Apache 2.4.49/2.4.50 Traversal Remote Code Execution Scanner
CGI Files ≈ Packet Storm Sep 1, 2024 | 16:28 pmThis Metasploit module scans for an unauthenticated RCE vulnerability which exists in Apache version 2.4.49 (CVE-2021-41773). If files outside of the document root are not protected by ‘require all denied’ and CGI has been explicitly enabled, it can be used[…]
Read more... -
Apache Mod_cgi Bash Environment Variable Injection (Shellshock) Scanner
CGI Files ≈ Packet Storm Sep 1, 2024 | 16:27 pmThis Metasploit module scans for the Shellshock vulnerability, a flaw in how the Bash shell handles external environment variables. This Metasploit module targets CGI scripts in the Apache web server by setting the HTTP_USER_AGENT environment variable to a malicious function[…]
Read more... -
Supermicro Onboard IPMI Url_redirect.cgi Authenticated Directory Traversal
CGI Files ≈ Packet Storm Sep 1, 2024 | 16:15 pmThis Metasploit module abuses a directory traversal vulnerability in the url_redirect.cgi application accessible through the web interface of Supermicro Onboard IPMI controllers. The vulnerability is present due to a lack of sanitization of the url_name parameter. This allows an attacker[…]
Read more... -
ZyXEL GS1510-16 Password Extractor
CGI Files ≈ Packet Storm Aug 31, 2024 | 21:44 pmThis Metasploit module exploits a vulnerability in ZyXEL GS1510-16 routers to extract the admin password. Due to a lack of authentication on the webctrl.cgi script, unauthenticated attackers can recover the administrator password for these devices. The vulnerable device has reached[…]
Read more... -
Sophos Web Protection Appliance Patience.cgi Directory Traversal
CGI Files ≈ Packet Storm Aug 31, 2024 | 21:35 pmThis Metasploit module abuses a directory traversal in Sophos Web Protection Appliance, specifically on the /cgi-bin/patience.cgi component. This Metasploit module has been tested successfully on the Sophos Web Virtual Appliance v3.7.0.
Read more...
snaplitics made a real revolution in the industry.
-
ABB Cylon Aspect 3.08.02 logYumLookup.php Authenticated File Disclosure
PHP Files ≈ Packet Storm Oct 24, 2024 | 13:44 pmABB Cylon Aspect version 3.08.02 suffers from an authenticated arbitrary file disclosure vulnerability. Input passed through the logFile GET parameter via the logYumLookup.php script is not properly verified before being used to download log files. This can be exploited to[…]
Read more... -
pfSense 2.5.2 Cross Site Scripting
PHP Files ≈ Packet Storm Oct 24, 2024 | 13:31 pmA cross site scripting vulnerability in pfsense version 2.5.2 allows attackers to execute arbitrary web scripts or HTML via a crafted payload injected into the $pconfig variable at interfaces_groups_edit.php.
Read more... -
ABB Cylon Aspect 3.08.01 persistenceManagerAjax.php Command Injection
PHP Files ≈ Packet Storm Oct 22, 2024 | 15:49 pmABB Cylon Aspect version 3.08.01 suffers from an unauthenticated OS command injection vulnerability. This can be exploited to inject and execute arbitrary shell commands through the directory HTTP POST parameter called by the persistenceManagerAjax.php script.
Read more... -
Helper 0.1
PHP Files ≈ Packet Storm Oct 21, 2024 | 12:40 pmHelper is an enumerator written in PHP that helps identify directories on webservers that could be targets for things like cross site scripting, local file inclusion, remote shell upload, and remote SQL injection vulnerabilities.
Read more... -
Magento / Adobe Commerce Remote Code Execution
PHP Files ≈ Packet Storm Oct 18, 2024 | 14:25 pmThis Metasploit module uses a combination of an arbitrary file read (CVE-2024-34102) and a buffer overflow in glibc (CVE-2024-2961). It allows for unauthenticated remote code execution on various versions of Magento and Adobe Commerce (and earlier versions if the PHP[…]
Read more... -
ABB Cylon Aspect 3.08.01 databaseFileDelete.php Command Injection
PHP Files ≈ Packet Storm Oct 18, 2024 | 14:22 pmABB Cylon Aspect version 3.08.01 suffers from an unauthenticated OS command injection vulnerability. This can be exploited to inject and execute arbitrary shell commands through the file HTTP POST parameter called by the databaseFileDelete.php script.
Read more... -
ABB Cylon Aspect 3.08.01 networkDiagAjax.php Remote Network Utility Execution
PHP Files ≈ Packet Storm Oct 17, 2024 | 13:46 pmABB Cylon Aspect version 3.08.01 allows an unauthenticated attacker to perform network operations such as ping, traceroute, or nslookup on arbitrary hosts or IPs by sending a crafted GET request to networkDiagAjax.php. This could be exploited to interact with or[…]
Read more... -
ABB Cylon Aspect 3.08.01 mapConfigurationDownload.php Configuration Download
PHP Files ≈ Packet Storm Oct 16, 2024 | 14:31 pmABB Cylon Aspect version 3.08.01 suffers from an unauthenticated configuration download vulnerability. This can be exploited to download the SQLite DB that contains the configuration mappings information via the FTControlServlet by directly calling the mapConfigurationDownload.php script.
Read more... -
ABB Cylon Aspect 3.08.00 sslCertAjax.php Remote Command Execution
PHP Files ≈ Packet Storm Oct 15, 2024 | 14:19 pmABB Cylon Aspect version 3.08.00 suffers from an authenticated OS command injection vulnerability. This can be exploited to inject and execute arbitrary shell commands through the country, state, locality, organization, and hostname HTTP POST parameters called by the sslCertAjax.php script.
Read more... -
ABB Cylon Aspect 3.08.00 yumSettings.php Command Injection
PHP Files ≈ Packet Storm Oct 14, 2024 | 13:35 pmABB Cylon Aspect version 3.08.00 suffers from an authenticated OS command injection vulnerability. This can be exploited to inject and execute arbitrary shell commands through the PROXY HTTP POST parameter called by the yumSettings.php script.
Read more...
-
Red Hat Security Advisory 2024-8455-03
Operating System: RedHat ≈ Packet Storm Oct 25, 2024 | 15:13 pmRed Hat Security Advisory 2024-8455-03 - An update for edk2 is now available for Red Hat Enterprise Linux 8.6 Advanced Mission Critical Update Support, Red Hat Enterprise Linux 8.6 Update Services for SAP Solutions, and Red Hat Enterprise Linux 8.6[…]
Read more... -
Red Hat Security Advisory 2024-8461-03
Operating System: RedHat ≈ Packet Storm Oct 25, 2024 | 15:13 pmRed Hat Security Advisory 2024-8461-03 - An update for krb5 is now available for Red Hat Enterprise Linux 9.2 Extended Update Support.
Read more... -
Red Hat Security Advisory 2024-8260-03
Operating System: RedHat ≈ Packet Storm Oct 25, 2024 | 15:12 pmRed Hat Security Advisory 2024-8260-03 - Red Hat OpenShift Container Platform release 4.16.18 is now available with updates to packages and images that fix several bugs and add enhancements. Issues addressed include a denial of service vulnerability.
Read more... -
Red Hat Security Advisory 2024-8263-03
Operating System: RedHat ≈ Packet Storm Oct 25, 2024 | 15:12 pmRed Hat Security Advisory 2024-8263-03 - Red Hat OpenShift Container Platform release 4.16.18 is now available with updates to packages and images that fix several bugs and add enhancements.
Read more... -
Red Hat Security Advisory 2024-8446-03
Operating System: RedHat ≈ Packet Storm Oct 25, 2024 | 15:12 pmRed Hat Security Advisory 2024-8446-03 - An update for python3.9 is now available for Red Hat Enterprise Linux 9.4 Extended Update Support.
Read more... -
Red Hat Security Advisory 2024-8447-03
Operating System: RedHat ≈ Packet Storm Oct 25, 2024 | 15:12 pmRed Hat Security Advisory 2024-8447-03 - An update for python3.12 is now available for Red Hat Enterprise Linux 9.4 Extended Update Support.
Read more... -
Red Hat Security Advisory 2024-8449-03
Operating System: RedHat ≈ Packet Storm Oct 25, 2024 | 15:12 pmRed Hat Security Advisory 2024-8449-03 - An update for edk2 is now available for Red Hat Enterprise Linux 8.4 Advanced Mission Critical Update Support, Red Hat Enterprise Linux 8.4 Telecommunications Update Service, and Red Hat Enterprise Linux 8.4 Update Services[…]
Read more... -
Red Hat Security Advisory 2024-8238-03
Operating System: RedHat ≈ Packet Storm Oct 24, 2024 | 13:23 pmRed Hat Security Advisory 2024-8238-03 - Red Hat OpenShift Container Platform release 4.14.39 is now available with updates to packages and images that fix several bugs and add enhancements.
Read more... -
Red Hat Security Advisory 2024-8365-03
Operating System: RedHat ≈ Packet Storm Oct 24, 2024 | 13:23 pmRed Hat Security Advisory 2024-8365-03 - An update for python-idna is now available for Red Hat Enterprise Linux 7 Extended Lifecycle Support. Issues addressed include a denial of service vulnerability.
Read more... -
Red Hat Security Advisory 2024-8374-03
Operating System: RedHat ≈ Packet Storm Oct 24, 2024 | 13:23 pmRed Hat Security Advisory 2024-8374-03 - An update for python3.11 is now available for Red Hat Enterprise Linux 9.4 Extended Update Support.
Read more... -
The Product Security Blog has moved!
Red Hat Security Blog Blog Posts Mar 19, 2019 | 19:38 pmRed Hat Product Security has joined forces with other security teams inside Red Hat to publish our content in a common venue using the Security channel of the Red Hat Blog.This move provides a wider variety of important Security topics,[…]
Read more... -
New Red Hat Product Security OpenPGP key
Red Hat Security Blog Blog Posts Aug 22, 2018 | 13:30 pmRed Hat Product Security has transitioned from using its old 1024-bit DSA OpenPGP key to a new 4096-bit RSA OpenPGP key.This was done to improve the long-term security of our communications with our customers and also to meet current key[…]
Read more... -
SPECTRE Variant 1 scanning tool
Red Hat Security Blog Blog Posts Jul 18, 2018 | 13:30 pmAs part of Red Hat's commitment to product security we have developed a tool internally that can be used to scan for variant 1 SPECTRE vulnerabilities. As part of our commitment to the wider user community, we are introducing this[…]
Read more... -
Red Hat’s disclosure process
Red Hat Security Blog Blog Posts Jul 10, 2018 | 13:00 pmLast week, a vulnerability (CVE-2018-10892) that affected CRI-O, Buildah, Podman, and Docker was made public before some affected upstream projects were notified. We regret that this was not handled in a way that lives up to our own standards around[…]
Read more... -
Join us in San Francisco at the 2018 Red Hat Summit
Red Hat Security Blog Blog Posts Apr 23, 2018 | 14:30 pmThis year’s Red Hat Summit will be held on May 8-10 in beautiful San Francisco, USA.Product Security will be joining many Red Hat security experts in presenting and assisting subscribers and partners at the show.Here is a sneak peek at[…]
Read more... -
Certificate Transparency and HTTPS
Red Hat Security Blog Blog Posts Apr 17, 2018 | 15:00 pmGoogle has announced that on April 30, 2018, Chrome will:“...require that all TLS server certificates issued after 30 April, 2018 be compliant with the Chromium CT Policy. After this date, when Chrome connects to a site serving a publicly-trusted certificate[…]
Read more... -
Let's talk about PCI-DSS
Red Hat Security Blog Blog Posts Feb 28, 2018 | 14:30 pmFor those who aren’t familiar with Payment Card Industry Data Security Standard (PCI-DSS), it is the standard that is intended to protect our credit card data as it flows between systems and is stored in company databases.PCI-DSS requires that all[…]
Read more... -
Security is from Mars, Developers are from Venus…...or ARE they?
Red Hat Security Blog Blog Posts Nov 16, 2017 | 15:00 pmIt is a tale as old as time.Developers and security personnel view each other withsuspicion.The perception is that a vast gulf of understanding and ability lies between the two camps.“They can’t possibly understand what it is to do my job!”[…]
Read more... -
Abuse of RESTEasy Default Providers in JBoss EAP
Red Hat Security Blog Blog Posts Oct 18, 2017 | 13:30 pmRed Hat JBoss Enterprise Application Platform (EAP) is a commonly used host for Restful webservices. A powerful but potentially dangerous feature of Restful webservices on JBoss EAP is the ability to accept any media type. If not configured to accept[…]
Read more... -
Kernel Stack Protector and BlueBorne
Red Hat Security Blog Blog Posts Sep 12, 2017 | 11:51 amToday, a security issue called BlueBorne was disclosed, a vulnerability that could be used to attack sensitive systems via the Bluetooth protocol. Specifically, BlueBorne is a flaw where a remote (but physically quite close) attacker could get root on a[…]
Read more...
-
Debian: DSA-5797-1: twisted Security Advisory Updates
Stay Vigilant with Timely Linux Security Advisories Oct 25, 2024 | 18:12 pm
Read more... Multiple security issues were found in Twisted, an event-based framework for internet applications, which could result in incorrect ordering of HTTP requests or cross-site scripting.
Multiple security issues were found in Twisted, an event-based framework for internet applications, which could result in incorrect ordering of HTTP requests or cross-site scripting. -
Debian: DSA-5796-1: libheif Security Advisory Updates
Stay Vigilant with Timely Linux Security Advisories Oct 25, 2024 | 18:10 pm
Read more... Multiple security issues were found in libheif, a library to parse HEIF and AVIF files, which could result in denial of service or potentially the execution of arbitrary code.
Multiple security issues were found in libheif, a library to parse HEIF and AVIF files, which could result in denial of service or potentially the execution of arbitrary code. -
Debian Security Advisory 5794-1
Operating System: Debian ≈ Packet Storm Oct 22, 2024 | 15:51 pmDebian Linux Security Advisory 5794-1 - Several vulnerabilities have been discovered in the OpenJDK Java runtime, which may result in denial of service or information disclosure.
Read more... -
Debian Security Advisory 5795-1
Operating System: Debian ≈ Packet Storm Oct 22, 2024 | 15:51 pmDebian Linux Security Advisory 5795-1 - Cedric Krier discovered that python-sql, a library to write SQL queries in a pythonic way, performed insufficient sanitizing which could result in SQL injection.
Read more... -
Debian: DSA-5795-1: python-sql Security Advisory Updates
Stay Vigilant with Timely Linux Security Advisories Oct 21, 2024 | 20:55 pm
Read more... Cedric Krier discovered that python-sql, a library to write SQL queries in a pythonic way, performed insufficient sanitising which could result in SQL injection.
Cedric Krier discovered that python-sql, a library to write SQL queries in a pythonic way, performed insufficient sanitising which could result in SQL injection. -
Debian: DSA-5794-1: openjdk-17 Security Advisory Updates
Stay Vigilant with Timely Linux Security Advisories Oct 21, 2024 | 18:19 pm
Read more... Several vulnerabilities have been discovered in the OpenJDK Java runtime, which may result in denial of service or information disclosure. For the stable distribution (bookworm), these problems have been fixed in
Several vulnerabilities have been discovered in the OpenJDK Java runtime, which may result in denial of service or information disclosure. For the stable distribution (bookworm), these problems have been fixed in -
Debian Security Advisory 5793-1
Operating System: Debian ≈ Packet Storm Oct 21, 2024 | 12:46 pmDebian Linux Security Advisory 5793-1 - Security issues were discovered in Chromium which could result in the execution of arbitrary code, denial of service, or information disclosure.
Read more... -
Debian: DSA-5793-1: chromium Security Advisory Updates
Stay Vigilant with Timely Linux Security Advisories Oct 20, 2024 | 07:45 am
Read more... Security issues were discovered in Chromium which could result in the execution of arbitrary code, denial of service, or information disclosure.
Security issues were discovered in Chromium which could result in the execution of arbitrary code, denial of service, or information disclosure. -
Debian Security Advisory 5792-1
Operating System: Debian ≈ Packet Storm Oct 15, 2024 | 14:22 pmDebian Linux Security Advisory 5792-1 - The following vulnerabilities have been discovered in the WebKitGTK web engine. Hafiizh and YoKo Kho discovered that visiting a malicious website may lead to address bar spoofing. Narendra Bhati discovered that a malicious website[…]
Read more... -
Debian: DSA-5792-1: webkit2gtk Security Advisory Updates
Stay Vigilant with Timely Linux Security Advisories Oct 14, 2024 | 21:53 pm
Read more... The following vulnerabilities have been discovered in the WebKitGTK web engine: CVE-2024-40866
The following vulnerabilities have been discovered in the WebKitGTK web engine: CVE-2024-40866 -
Debian Security Advisory 5791-1
Operating System: Debian ≈ Packet Storm Oct 14, 2024 | 13:43 pmDebian Linux Security Advisory 5791-1 - Elyas Damej discovered that a sandbox mechanism in ReportLab, a Python library to create PDF documents, could be bypassed which may result in the execution of arbitrary code when converting malformed HTML to a[…]
Read more... -
Debian Security Advisory 5790-1
Operating System: Debian ≈ Packet Storm Oct 14, 2024 | 13:34 pmDebian Linux Security Advisory 5790-1 - It was discovered that DOMPurify, a sanitizer for HTML, MathML and SVG was susceptible to nesting-based mXSS.
Read more... -
Debian Security Advisory 5789-1
Operating System: Debian ≈ Packet Storm Oct 14, 2024 | 13:31 pmDebian Linux Security Advisory 5789-1 - Multiple security issues were discovered in Thunderbird, which could result in the execution of arbitrary code.
Read more... -
Debian: DSA-5791-1: python-reportlab Security Advisory Updates
Stay Vigilant with Timely Linux Security Advisories Oct 13, 2024 | 18:22 pm
Read more... Elyas Damej discovered that a sandbox mechanism in ReportLab, a Python library to create PDF documents, could be bypassed which may result in the execution of arbitrary code when converting malformed HTML to a PDF document.
Elyas Damej discovered that a sandbox mechanism in ReportLab, a Python library to create PDF documents, could be bypassed which may result in the execution of arbitrary code when converting malformed HTML to a PDF document. -
Debian: DSA-5790-1: node-dompurify Security Advisory Updates
Stay Vigilant with Timely Linux Security Advisories Oct 13, 2024 | 17:58 pm
Read more... It was discovered that DOMPurify, a sanitizer for HTML, MathML and SVG was susceptible to nesting-based mXSS. For the stable distribution (bookworm), this problem has been fixed in
It was discovered that DOMPurify, a sanitizer for HTML, MathML and SVG was susceptible to nesting-based mXSS. For the stable distribution (bookworm), this problem has been fixed in -
Debian: DSA-5789-1: thunderbird Security Advisory Updates
Stay Vigilant with Timely Linux Security Advisories Oct 12, 2024 | 10:18 am
Read more... Multiple security issues were discovered in Thunderbird, which could result in the execution of arbitrary code. For the stable distribution (bookworm), these problems have been fixed in
Multiple security issues were discovered in Thunderbird, which could result in the execution of arbitrary code. For the stable distribution (bookworm), these problems have been fixed in -
Debian Security Advisory 5788-1
Operating System: Debian ≈ Packet Storm Oct 11, 2024 | 15:11 pmDebian Linux Security Advisory 5788-1 - Damien Schaeffer discovered a use-after-free in the Mozilla Firefox web browser, which could result in the execution of arbitrary code.
Read more... -
Debian: DSA-5788-1: firefox-esr Security Advisory Updates
Stay Vigilant with Timely Linux Security Advisories Oct 10, 2024 | 16:21 pm
Read more... Damien Schaeffer discovered a use-after-free in the Mozilla Firefox web browser, which could result in the execution of arbitrary code. For the stable distribution (bookworm), this problem has been fixed in
Damien Schaeffer discovered a use-after-free in the Mozilla Firefox web browser, which could result in the execution of arbitrary code. For the stable distribution (bookworm), this problem has been fixed in -
Debian Security Advisory 5787-1
Operating System: Debian ≈ Packet Storm Oct 10, 2024 | 14:05 pmDebian Linux Security Advisory 5787-1 - Security issues were discovered in Chromium which could result in the execution of arbitrary code, denial of service, or information disclosure.
Read more... -
Debian Security Advisory 5729-2
Operating System: Debian ≈ Packet Storm Oct 9, 2024 | 14:04 pmDebian Linux Security Advisory 5729-2 - The fixes for CVE-2024-38474 and CVE-2024-39884 introduced two regressions in mod_rewrite and mod_proxy.
Read more...
-
Ubuntu Security Notice USN-7082-1
Operating System: Ubuntu ≈ Packet Storm Oct 23, 2024 | 14:32 pmUbuntu Security Notice 7082-1 - Gerrard Tai discovered that libheif did not properly validate certain images, leading to out-of-bounds read and write vulnerability. If a user or automated system were tricked into opening a specially crafted file, an attacker could[…]
Read more... -
Ubuntu Security Notice USN-7079-1
Operating System: Ubuntu ≈ Packet Storm Oct 23, 2024 | 14:31 pmUbuntu Security Notice 7079-1 - Several security issues were discovered in the WebKitGTK Web and JavaScript engines. If a user were tricked into viewing a malicious website, a remote attacker could exploit a variety of issues related to web browser[…]
Read more... -
Ubuntu Security Notice USN-7081-1
Operating System: Ubuntu ≈ Packet Storm Oct 23, 2024 | 14:31 pmUbuntu Security Notice 7081-1 - It was discovered that the Go net/http module did not properly handle responses to requests with an "Expect: 100-continue" header under certain circumstances. An attacker could possibly use this issue to cause a denial of[…]
Read more... -
Ubuntu Security Notice USN-7080-1
Operating System: Ubuntu ≈ Packet Storm Oct 22, 2024 | 15:44 pmUbuntu Security Notice 7080-1 - Toshifumi Sakaguchi discovered that Unbound incorrectly handled name compression for large RRsets, which could lead to excessive CPU usage. An attacker could potentially use this issue to cause a denial of service by sending specially[…]
Read more... -
Ubuntu Security Notice USN-7072-2
Operating System: Ubuntu ≈ Packet Storm Oct 22, 2024 | 15:43 pmUbuntu Security Notice 7072-2 - Several security issues were discovered in the Linux kernel. An attacker could possibly use these to compromise the system.
Read more... -
Ubuntu Security Notice USN-7078-1
Operating System: Ubuntu ≈ Packet Storm Oct 22, 2024 | 15:43 pmUbuntu Security Notice 7078-1 - Atte Kettunen discovered that Firefox did not properly validate before inserting ranges into the selection node cache. An attacker could possibly use this issue to cause a denial of service or execute arbitrary code.
Read more... -
Ubuntu Security Notice USN-7062-2
Operating System: Ubuntu ≈ Packet Storm Oct 22, 2024 | 15:42 pmUbuntu Security Notice 7062-2 - USN-7062-1 fixed vulnerabilities in libgsf. This update provides the corresponding updates for Ubuntu 24.10. It was discovered that libgsf incorrectly handled certain Compound Document Binary files. If a user or automated system were tricked into[…]
Read more... -
Ubuntu Security Notice USN-7042-3
Operating System: Ubuntu ≈ Packet Storm Oct 22, 2024 | 15:34 pmUbuntu Security Notice 7042-3 - USN-7042-2 released an improved fix for cups-browsed. This update provides the corresponding update for Ubuntu 24.10. Simone Margaritelli discovered that cups-browsed could be used to create arbitrary printers from outside the local network. In combination[…]
Read more... -
Ubuntu Security Notice USN-7077-1
Operating System: Ubuntu ≈ Packet Storm Oct 21, 2024 | 12:54 pmUbuntu Security Notice 7077-1 - Enrique Nissim and Krzysztof Okupski discovered that some AMD processors did not properly restrict access to the System Management Mode configuration when the SMM Lock was enabled. A privileged local attacker could possibly use this[…]
Read more... -
Ubuntu Security Notice USN-7076-1
Operating System: Ubuntu ≈ Packet Storm Oct 18, 2024 | 14:11 pmUbuntu Security Notice 7076-1 - Several security issues were discovered in the Linux kernel. An attacker could possibly use these to compromise the system.
Read more...
-
chromium -- multiple security fixes
FreeBSD VuXML Oct 26, 2024 | 00:00 am
Read more... -
chromium -- multiple security fixes
FreeBSD VuXML Oct 26, 2024 | 00:00 am
Read more... -
Gitlab -- vulnerabilities
FreeBSD VuXML Oct 24, 2024 | 00:00 am
Read more... -
electron31 -- multiple vulnerabilities
FreeBSD VuXML Oct 24, 2024 | 00:00 am
Read more... -
electron32 -- multiple vulnerabilities
FreeBSD VuXML Oct 23, 2024 | 00:00 am
Read more... -
OpenSSL -- OOB memory access vulnerability
FreeBSD VuXML Oct 19, 2024 | 00:00 am
Read more...