Service (16)
Children categories
Security News (14)

Im Sinne der Aktualität sind diese News grösstenteils in englischer Sprache. Falls nötig, bitte die Übersetzungsfunktion verwenden.
View items...Workshops (2)

Installationen, Konfigurationen mit Bildern und Videos verständlich erklärt
View items...-
Red Hat Security Advisory 2024-4542-03
Ruby Files ≈ Packet Storm Jul 15, 2024 | 20:36 pmRed Hat Security Advisory 2024-4542-03 - An update for ruby is now available for Red Hat Enterprise Linux 9.2 Extended Update Support. Issues addressed include a HTTP response splitting vulnerability.
Read more... -
Red Hat Security Advisory 2024-4499-03
Ruby Files ≈ Packet Storm Jul 11, 2024 | 14:04 pmRed Hat Security Advisory 2024-4499-03 - An update for ruby is now available for Red Hat Enterprise Linux 8. Issues addressed include a denial of service vulnerability.
Read more... -
Ubuntu Security Notice USN-6853-1
Ruby Files ≈ Packet Storm Jun 27, 2024 | 14:38 pmUbuntu Security Notice 6853-1 - It was discovered that Ruby incorrectly handled the ungetbyte and ungetc methods. A remote attacker could use this issue to cause Ruby to crash, resulting in a denial of service, or possibly obtain sensitive information.
Read more... -
Ubuntu Security Notice USN-6838-1
Ruby Files ≈ Packet Storm Jun 17, 2024 | 15:16 pmUbuntu Security Notice 6838-1 - It was discovered that Ruby RDoc incorrectly parsed certain YAML files. If a user or automated system were tricked into parsing a specially crafted .rdoc_options file, a remote attacker could possibly use this issue to[…]
Read more... -
Red Hat Security Advisory 2024-3838-03
Ruby Files ≈ Packet Storm Jun 12, 2024 | 13:49 pmRed Hat Security Advisory 2024-3838-03 - An update for ruby is now available for Red Hat Enterprise Linux 9. Issues addressed include HTTP response splitting and denial of service vulnerabilities.
Read more... -
Red Hat Security Advisory 2024-3670-03
Ruby Files ≈ Packet Storm Jun 6, 2024 | 18:58 pmRed Hat Security Advisory 2024-3670-03 - An update for the ruby:3.3 module is now available for Red Hat Enterprise Linux 8.
Read more... -
Red Hat Security Advisory 2024-3671-03
Ruby Files ≈ Packet Storm Jun 6, 2024 | 18:58 pmRed Hat Security Advisory 2024-3671-03 - An update for the ruby:3.3 module is now available for Red Hat Enterprise Linux 9.
Read more... -
Red Hat Security Advisory 2024-3668-03
Ruby Files ≈ Packet Storm Jun 6, 2024 | 18:57 pmRed Hat Security Advisory 2024-3668-03 - An update for the ruby:3.1 module is now available for Red Hat Enterprise Linux 9.
Read more... -
Red Hat Security Advisory 2024-3546-03
Ruby Files ≈ Packet Storm Jun 4, 2024 | 13:35 pmRed Hat Security Advisory 2024-3546-03 - An update for the ruby:3.1 module is now available for Red Hat Enterprise Linux 8.
Read more... -
Red Hat Security Advisory 2024-3500-03
Ruby Files ≈ Packet Storm May 31, 2024 | 16:08 pmRed Hat Security Advisory 2024-3500-03 - An update for the ruby:3.0 module is now available for Red Hat Enterprise Linux 8. Issues addressed include HTTP response splitting and denial of service vulnerabilities.
Read more...
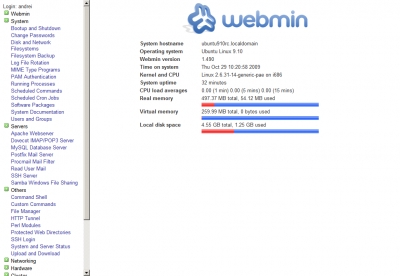
Diese Module beschreiben alles, was mit der Administration des Grundsystems verbunden ist. Dazu gehören zum Beispiel Startverhalten, Anwenderverwaltung, Software-Installation und derzeit laufende Prozesse.
Vorbereitung und Installation
Um Webmin auf Ihrem System laufen zu lassen, benötigen Sie einige Pakete, die eventuell in der Standardinstallation Ihrer Distribution nicht vorhanden sind. Mittels yum, apt und Konsorten ist es aber ein Leichtes, diese Packages nachzuziehen. Vor allen Dingen lösen yum und apt die Abhängigkeiten von selbst auf und installieren selbstständig alles Notwendige.
-
Ubuntu Security Notice USN-6906-1
Python Files ≈ Packet Storm Jul 24, 2024 | 13:37 pmUbuntu Security Notice 6906-1 - It was discovered that python-zipp did not properly handle the zip files with malformed names. An attacker could possibly use this issue to cause a denial of service.
Read more... -
Ubuntu Security Notice USN-6891-1
Python Files ≈ Packet Storm Jul 11, 2024 | 14:08 pmUbuntu Security Notice 6891-1 - It was discovered that Python incorrectly handled certain inputs. An attacker could possibly use this issue to execute arbitrary code. This issue only affected Ubuntu 14.04 LTS and Ubuntu 18.04 LTS. It was discovered that[…]
Read more... -
Red Hat Security Advisory 2024-4260-03
Python Files ≈ Packet Storm Jul 3, 2024 | 15:05 pmRed Hat Security Advisory 2024-4260-03 - An update for python-idna is now available for Red Hat Enterprise Linux 8. Issues addressed include a denial of service vulnerability.
Read more... -
Red Hat Security Advisory 2024-4231-03
Python Files ≈ Packet Storm Jul 3, 2024 | 15:03 pmRed Hat Security Advisory 2024-4231-03 - An update for python-jinja2 is now available for Red Hat Enterprise Linux 8.
Read more... -
Red Hat Security Advisory 2024-4227-03
Python Files ≈ Packet Storm Jul 3, 2024 | 15:02 pmRed Hat Security Advisory 2024-4227-03 - An update for python-pillow is now available for Red Hat Enterprise Linux 8. Issues addressed include a buffer overflow vulnerability.
Read more... -
Red Hat Security Advisory 2024-4053-03
Python Files ≈ Packet Storm Jun 24, 2024 | 12:46 pmRed Hat Security Advisory 2024-4053-03 - An update for python-yaql, openstack-tripleo-heat-templates, and openstack-tripleo-common is now available for Red Hat OpenStack Platform 16.2. Issues addressed include an information leakage vulnerability.
Read more... -
Red Hat Security Advisory 2024-4054-03
Python Files ≈ Packet Storm Jun 24, 2024 | 12:46 pmRed Hat Security Advisory 2024-4054-03 - An update for python-gunicorn is now available for Red Hat OpenStack Platform 16.2. Issues addressed include a HTTP request smuggling vulnerability.
Read more... -
Red Hat Security Advisory 2024-3846-03
Python Files ≈ Packet Storm Jun 12, 2024 | 13:51 pmRed Hat Security Advisory 2024-3846-03 - An update for python-idna is now available for Red Hat Enterprise Linux 9. Issues addressed include a denial of service vulnerability.
Read more... -
Debian Security Advisory 5704-1
Python Files ≈ Packet Storm Jun 6, 2024 | 19:00 pmDebian Linux Security Advisory 5704-1 - Multiple security issues were discovered in Pillow, a Python imaging library, which could result in denial of service or the execution of arbitrary code if malformed images are processed.
Read more... -
Red Hat Security Advisory 2024-3552-03
Python Files ≈ Packet Storm Jun 4, 2024 | 13:35 pmRed Hat Security Advisory 2024-3552-03 - An update for python-idna is now available for Red Hat Enterprise Linux 8.6. Issues addressed include a denial of service vulnerability.
Read more...
-
PHP CGI Argument Injection Remote Code Execution
CGI Files ≈ Packet Storm Jun 18, 2024 | 14:03 pmThis Metasploit module exploits a PHP CGI argument injection vulnerability affecting PHP in certain configurations on a Windows target. A vulnerable configuration is locale dependant (such as Chinese or Japanese), such that the Unicode best-fit conversion scheme will unexpectedly convert[…]
Read more... -
QNAP QTS / QuTS Hero Unauthenticated Remote Code Execution
CGI Files ≈ Packet Storm Feb 22, 2024 | 15:11 pmThere exists an unauthenticated command injection vulnerability in the QNAP operating system known as QTS and QuTS hero. QTS is a core part of the firmware for numerous QNAP entry and mid-level Network Attached Storage (NAS) devices, and QuTS hero[…]
Read more... -
Nikto Web Scanner 2.5.0
CGI Files ≈ Packet Storm Dec 4, 2023 | 15:02 pmNikto is an Open Source web server scanner which performs comprehensive tests against web servers for multiple items, including over 3500 potentially dangerous files/CGIs, versions on over 900 servers, and version specific problems on over 250 servers.
Read more... -
R Radio Network FM Transmitter 1.07 system.cgi Password Disclosure
CGI Files ≈ Packet Storm Dec 4, 2023 | 13:59 pmR Radio Network FM Transmitter version 1.07 suffers from an improper access control that allows an unauthenticated actor to directly reference the system.cgi endpoint and disclose the clear-text password of the admin user allowing authentication bypass and FM station setup[…]
Read more... -
Electrolink FM/DAB/TV Transmitter Unauthenticated Remote Denial Of Service
CGI Files ≈ Packet Storm Oct 2, 2023 | 15:35 pmElectrolink FM/DAB/TV Transmitter from a denial of service scenario. An unauthenticated attacker can reset the board as well as stop the transmitter operations by sending one GET request to the command.cgi gateway.
Read more... -
Lexmark Device Embedded Web Server Remote Code Execution
CGI Files ≈ Packet Storm Sep 19, 2023 | 15:57 pmAn unauthenticated remote code execution vulnerability exists in the embedded webserver in certain Lexmark devices through 2023-02-19. The vulnerability is only exposed if, when setting up the printer or device, the user selects "Set up Later" when asked if they[…]
Read more... -
Tinycontrol LAN Controller 3 Denial Of Service
CGI Files ≈ Packet Storm Sep 2, 2023 | 13:18 pmTinycontrol LAN Controller version 3 suffers from an unauthenticated remote denial of service vulnerability. An attacker can issue direct requests to the stm.cgi page to reboot and also reset factory settings on the device.
Read more... -
Western Digital MyCloud Unauthenticated Command Injection
CGI Files ≈ Packet Storm Jul 28, 2023 | 14:03 pmThis Metasploit module exploits authentication bypass (CVE-2018-17153) and command injection (CVE-2016-10108) vulnerabilities in Western Digital MyCloud before 2.30.196 in order to achieve unauthenticated remote code execution as the root user. The module first performs a check to see if the[…]
Read more... -
Ubuntu Security Notice USN-6181-1
CGI Files ≈ Packet Storm Jun 21, 2023 | 15:59 pmUbuntu Security Notice 6181-1 - Hiroshi Tokumaru discovered that Ruby did not properly handle certain user input for applications the generate HTTP responses using cgi gem. An attacker could possibly use this issue to maliciously modify the response a user[…]
Read more... -
SecurePoint UTM 12.x Memory Leak
CGI Files ≈ Packet Storm Apr 18, 2023 | 17:34 pmSecurePoint UTM versions 12.x suffers from a memory leak vulnerability via the spcgi.cgi endpoint.
Read more...
snaplitics made a real revolution in the industry.
-
PHP MaXiMuS 2.5.2 Cross Site Scripting
PHP Files ≈ Packet Storm Jul 23, 2024 | 12:09 pmPHP MaXiMuS version 2.5.2 suffers from a cross site scripting vulnerability.
Read more... -
Ubuntu Security Notice USN-6305-3
PHP Files ≈ Packet Storm Jul 4, 2024 | 15:05 pmUbuntu Security Notice 6305-3 - USN-6305-2 fixed a vulnerability in PHP. The update caused a regression in Ubuntu 16.04 LTS and Ubuntu 18.04 LTS. This update fix it. It was discovered that PHP incorrectly handled certain XML files. An attacker[…]
Read more... -
Ubuntu Security Notice USN-6841-1
PHP Files ≈ Packet Storm Jun 20, 2024 | 11:51 amUbuntu Security Notice 6841-1 - It was discovered that PHP could early return in the filter_var function resulting in invalid user information being treated as valid user information. An attacker could possibly use this issue to expose raw user input[…]
Read more... -
Debian Security Advisory 5715-1
PHP Files ≈ Packet Storm Jun 19, 2024 | 12:15 pmDebian Linux Security Advisory 5715-1 - Two vulnerabilities have been discovered in Composer, a dependency manager for PHP, which could result in arbitrary command execution by operating on malicious git/hg repositories.
Read more... -
PHP CGI Argument Injection Remote Code Execution
PHP Files ≈ Packet Storm Jun 18, 2024 | 14:03 pmThis Metasploit module exploits a PHP CGI argument injection vulnerability affecting PHP in certain configurations on a Windows target. A vulnerable configuration is locale dependant (such as Chinese or Japanese), such that the Unicode best-fit conversion scheme will unexpectedly convert[…]
Read more... -
PHP Remote Code Execution
PHP Files ≈ Packet Storm Jun 14, 2024 | 13:14 pmPHP versions prior to 8.3.8 suffer from a remote code execution vulnerability.
Read more... -
Cacti Import Packages Remote Code Execution
PHP Files ≈ Packet Storm Jun 13, 2024 | 12:58 pmThis exploit module leverages an arbitrary file write vulnerability in Cacti versions prior to 1.2.27 to achieve remote code execution. It abuses the Import Packages feature to upload a specially crafted package that embeds a PHP file. Cacti will extract[…]
Read more... -
Ubuntu Security Notice USN-6825-1
PHP Files ≈ Packet Storm Jun 11, 2024 | 13:27 pmUbuntu Security Notice 6825-1 - It was discovered that the PDO driver in ADOdb was incorrectly handling string quotes. A remote attacker could possibly use this issue to perform SQL injection attacks. This issue only affected Ubuntu 16.04 LTS. It[…]
Read more... -
WordPress Hash Form 1.1.0 Remote Code Execution
PHP Files ≈ Packet Storm Jun 6, 2024 | 18:46 pmThe Hash Form Drag and Drop Form Builder plugin for WordPress suffers from a critical vulnerability due to missing file type validation in the file_upload_action function. This vulnerability exists in all versions up to and including 1.1.0. Unauthenticated attackers can[…]
Read more... -
Aquatronica Control System 5.1.6 Password Disclosure
PHP Files ≈ Packet Storm May 30, 2024 | 14:14 pmAquatronica Control System version 5.1.6 has a tcp.php endpoint on the controller that is exposed to unauthenticated attackers over the network. This vulnerability allows remote attackers to send a POST request which can reveal sensitive configuration information, including plaintext passwords.[…]
Read more...
-
Red Hat Security Advisory 2024-4827-03
Operating System: RedHat ≈ Packet Storm Jul 25, 2024 | 13:15 pmRed Hat Security Advisory 2024-4827-03 - An update for the httpd:2.4 module is now available for Red Hat Enterprise Linux 8.6 Advanced Mission Critical Update Support, Red Hat Enterprise Linux 8.6 Update Services for SAP Solutions, and Red Hat Enterprise[…]
Read more... -
Red Hat Security Advisory 2024-4828-03
Operating System: RedHat ≈ Packet Storm Jul 25, 2024 | 13:15 pmRed Hat Security Advisory 2024-4828-03 - An update for freeradius is now available for Red Hat Enterprise Linux 9.2 Extended Update Support.
Read more... -
Red Hat Security Advisory 2024-4829-03
Operating System: RedHat ≈ Packet Storm Jul 25, 2024 | 13:15 pmRed Hat Security Advisory 2024-4829-03 - An update for the freeradius:3.0 module is now available for Red Hat Enterprise Linux 8.8 Extended Update Support.
Read more... -
Red Hat Security Advisory 2024-4830-03
Operating System: RedHat ≈ Packet Storm Jul 25, 2024 | 13:15 pmRed Hat Security Advisory 2024-4830-03 - An update for the httpd:2.4 module is now available for Red Hat Enterprise Linux 8.4 Advanced Mission Critical Update Support, Red Hat Enterprise Linux 8.4 Update Services for SAP Solutions, and Red Hat Enterprise[…]
Read more... -
Red Hat Security Advisory 2024-4831-03
Operating System: RedHat ≈ Packet Storm Jul 25, 2024 | 13:15 pmRed Hat Security Advisory 2024-4831-03 - An update for kernel-rt is now available for Red Hat Enterprise Linux 9.2 Extended Update Support.
Read more... -
Red Hat Security Advisory 2024-4836-03
Operating System: RedHat ≈ Packet Storm Jul 25, 2024 | 13:15 pmRed Hat Security Advisory 2024-4836-03 - Updated images are now available for Red Hat Advanced Cluster Security. The updated image includes new features, bug fixes, and updates to patch vulnerabilities.
Read more... -
Red Hat Security Advisory 2024-4823-03
Operating System: RedHat ≈ Packet Storm Jul 25, 2024 | 13:14 pmRed Hat Security Advisory 2024-4823-03 - An update for kernel is now available for Red Hat Enterprise Linux 9.2 Extended Update Support. Issues addressed include denial of service, double free, and information leakage vulnerabilities.
Read more... -
Red Hat Security Advisory 2024-4824-03
Operating System: RedHat ≈ Packet Storm Jul 25, 2024 | 13:14 pmRed Hat Security Advisory 2024-4824-03 - An update for the nodejs:18 module is now available for Red Hat Enterprise Linux 8.8 Extended Update Support. Issues addressed include a denial of service vulnerability.
Read more... -
Red Hat Security Advisory 2024-4825-03
Operating System: RedHat ≈ Packet Storm Jul 25, 2024 | 13:14 pmRed Hat Security Advisory 2024-4825-03 - An update for podman is now available for Red Hat Enterprise Linux 9.0 Update Services for SAP Solutions. Issues addressed include deserialization and memory exhaustion vulnerabilities.
Read more... -
Red Hat Security Advisory 2024-4826-03
Operating System: RedHat ≈ Packet Storm Jul 25, 2024 | 13:14 pmRed Hat Security Advisory 2024-4826-03 - An update for the freeradius:3.0 module is now available for Red Hat Enterprise Linux 8.6 Advanced Mission Critical Update Support, Red Hat Enterprise Linux 8.6 Update Services for SAP Solutions, and Red Hat Enterprise[…]
Read more... -
The Product Security Blog has moved!
Red Hat Security Blog Blog Posts Mar 19, 2019 | 19:38 pmRed Hat Product Security has joined forces with other security teams inside Red Hat to publish our content in a common venue using the Security channel of the Red Hat Blog.This move provides a wider variety of important Security topics,[…]
Read more... -
New Red Hat Product Security OpenPGP key
Red Hat Security Blog Blog Posts Aug 22, 2018 | 13:30 pmRed Hat Product Security has transitioned from using its old 1024-bit DSA OpenPGP key to a new 4096-bit RSA OpenPGP key.This was done to improve the long-term security of our communications with our customers and also to meet current key[…]
Read more... -
SPECTRE Variant 1 scanning tool
Red Hat Security Blog Blog Posts Jul 18, 2018 | 13:30 pmAs part of Red Hat's commitment to product security we have developed a tool internally that can be used to scan for variant 1 SPECTRE vulnerabilities. As part of our commitment to the wider user community, we are introducing this[…]
Read more... -
Red Hat’s disclosure process
Red Hat Security Blog Blog Posts Jul 10, 2018 | 13:00 pmLast week, a vulnerability (CVE-2018-10892) that affected CRI-O, Buildah, Podman, and Docker was made public before some affected upstream projects were notified. We regret that this was not handled in a way that lives up to our own standards around[…]
Read more... -
Join us in San Francisco at the 2018 Red Hat Summit
Red Hat Security Blog Blog Posts Apr 23, 2018 | 14:30 pmThis year’s Red Hat Summit will be held on May 8-10 in beautiful San Francisco, USA.Product Security will be joining many Red Hat security experts in presenting and assisting subscribers and partners at the show.Here is a sneak peek at[…]
Read more... -
Certificate Transparency and HTTPS
Red Hat Security Blog Blog Posts Apr 17, 2018 | 15:00 pmGoogle has announced that on April 30, 2018, Chrome will:“...require that all TLS server certificates issued after 30 April, 2018 be compliant with the Chromium CT Policy. After this date, when Chrome connects to a site serving a publicly-trusted certificate[…]
Read more... -
Let's talk about PCI-DSS
Red Hat Security Blog Blog Posts Feb 28, 2018 | 14:30 pmFor those who aren’t familiar with Payment Card Industry Data Security Standard (PCI-DSS), it is the standard that is intended to protect our credit card data as it flows between systems and is stored in company databases.PCI-DSS requires that all[…]
Read more... -
Security is from Mars, Developers are from Venus…...or ARE they?
Red Hat Security Blog Blog Posts Nov 16, 2017 | 15:00 pmIt is a tale as old as time.Developers and security personnel view each other withsuspicion.The perception is that a vast gulf of understanding and ability lies between the two camps.“They can’t possibly understand what it is to do my job!”[…]
Read more... -
Abuse of RESTEasy Default Providers in JBoss EAP
Red Hat Security Blog Blog Posts Oct 18, 2017 | 13:30 pmRed Hat JBoss Enterprise Application Platform (EAP) is a commonly used host for Restful webservices. A powerful but potentially dangerous feature of Restful webservices on JBoss EAP is the ability to accept any media type. If not configured to accept[…]
Read more... -
Kernel Stack Protector and BlueBorne
Red Hat Security Blog Blog Posts Sep 12, 2017 | 11:51 amToday, a security issue called BlueBorne was disclosed, a vulnerability that could be used to attack sensitive systems via the Bluetooth protocol. Specifically, BlueBorne is a flaw where a remote (but physically quite close) attacker could get root on a[…]
Read more...
-
Debian: DSA-5734-1: bind9 Security Advisory Updates
Stay Vigilant with Timely Linux Security Advisories Jul 25, 2024 | 21:57 pm
Read more... Several vulnerabilities were discovered in BIND, a DNS server implementation, which may result in denial of service. To mitigate CVE-2024-1737 two new configuration statements have been
Several vulnerabilities were discovered in BIND, a DNS server implementation, which may result in denial of service. To mitigate CVE-2024-1737 two new configuration statements have been -
Debian Security Advisory 5733-1
Operating System: Debian ≈ Packet Storm Jul 19, 2024 | 13:39 pmDebian Linux Security Advisory 5733-1 - Multiple security issues were discovered in Thunderbird, which could potentially result in the execution of arbitrary code.
Read more... -
Debian: DSA-5733-1: thunderbird Security Advisory Updates
Stay Vigilant with Timely Linux Security Advisories Jul 18, 2024 | 20:50 pm
Read more... Multiple security issues were discovered in Thunderbird, which could potentially result in the execution of arbitrary code. For the oldstable distribution (bullseye), these problems have been fixed
Multiple security issues were discovered in Thunderbird, which could potentially result in the execution of arbitrary code. For the oldstable distribution (bullseye), these problems have been fixed -
Debian Security Advisory 5732-1
Operating System: Debian ≈ Packet Storm Jul 18, 2024 | 13:59 pmDebian Linux Security Advisory 5732-1 - Security issues were discovered in Chromium which could result in the execution of arbitrary code, denial of service, or information disclosure.
Read more... -
Debian: DSA-5732-1: chromium Security Advisory Updates
Stay Vigilant with Timely Linux Security Advisories Jul 18, 2024 | 06:25 am
Read more... Security issues were discovered in Chromium which could result in the execution of arbitrary code, denial of service, or information disclosure.
Security issues were discovered in Chromium which could result in the execution of arbitrary code, denial of service, or information disclosure. -
Debian Security Advisory 5731-1
Operating System: Debian ≈ Packet Storm Jul 17, 2024 | 17:30 pmDebian Linux Security Advisory 5731-1 - Several vulnerabilities have been discovered in the Linux kernel that may lead to a privilege escalation, denial of service or information leaks.
Read more... -
Debian: DSA-5731-1: linux Security Advisory Updates
Stay Vigilant with Timely Linux Security Advisories Jul 16, 2024 | 20:58 pm
Read more... Several vulnerabilities have been discovered in the Linux kernel that may lead to a privilege escalation, denial of service or information leaks.
Several vulnerabilities have been discovered in the Linux kernel that may lead to a privilege escalation, denial of service or information leaks. -
Debian Security Advisory 5730-1
Operating System: Debian ≈ Packet Storm Jul 16, 2024 | 15:21 pmDebian Linux Security Advisory 5730-1 - Several vulnerabilities have been discovered in the Linux kernel that may lead to a privilege escalation, denial of service or information leaks.
Read more... -
Debian: DSA-5730-1: linux Security Advisory Updates
Stay Vigilant with Timely Linux Security Advisories Jul 15, 2024 | 20:09 pm
Read more... Several vulnerabilities have been discovered in the Linux kernel that may lead to a privilege escalation, denial of service or information leaks.
Several vulnerabilities have been discovered in the Linux kernel that may lead to a privilege escalation, denial of service or information leaks. -
Debian Security Advisory 5729-1
Operating System: Debian ≈ Packet Storm Jul 12, 2024 | 14:37 pmDebian Linux Security Advisory 5729-1 - Multiple vulnerabilities have been discovered in the Apache HTTP server, which may result in authentication bypass, execution of scripts in directories not directly reachable by any URL, server-side request forgery or denial of service.
Read more... -
Debian: DSA-5729-1: apache2 Security Advisory Updates
Stay Vigilant with Timely Linux Security Advisories Jul 11, 2024 | 19:40 pm
Read more... Multiple vulnerabilities have been discovered in the Apache HTTP server, which may result in authentication bypass, execution of scripts in directories not directly reachable by any URL, server-side request forgery or denial of service.
Multiple vulnerabilities have been discovered in the Apache HTTP server, which may result in authentication bypass, execution of scripts in directories not directly reachable by any URL, server-side request forgery or denial of service. -
Debian Security Advisory 5727-1
Operating System: Debian ≈ Packet Storm Jul 11, 2024 | 14:10 pmDebian Linux Security Advisory 5727-1 - Multiple security issues have been found in the Mozilla Firefox web browser, which could potentially result in the execution of arbitrary code or privilege escalation.
Read more... -
Debian Security Advisory 5728-1
Operating System: Debian ≈ Packet Storm Jul 11, 2024 | 14:10 pmDebian Linux Security Advisory 5728-1 - Phillip Szelat discovered that Exim, a mail transport agent, does not properly parse a multiline RFC 2231 header filename, allowing a remote attacker to bypass a $mime_filename based extension-blocking protection mechanism.
Read more... -
Debian: DSA-5728-1: exim4 Security Advisory Updates
Stay Vigilant with Timely Linux Security Advisories Jul 10, 2024 | 20:28 pm
Read more... Phillip Szelat discovered that Exim, a mail transport agent, does not properly parse a multiline RFC 2231 header filename, allowing a remote attacker to bypass a $mime_filename based extension-blocking protection mechanism.
Phillip Szelat discovered that Exim, a mail transport agent, does not properly parse a multiline RFC 2231 header filename, allowing a remote attacker to bypass a $mime_filename based extension-blocking protection mechanism. -
Debian: DSA-5727-1: firefox-esr Security Advisory Updates
Stay Vigilant with Timely Linux Security Advisories Jul 10, 2024 | 20:21 pm
Read more... Multiple security issues have been found in the Mozilla Firefox web browser, which could potentially result in the execution of arbitrary code or privilege escalation.
Multiple security issues have been found in the Mozilla Firefox web browser, which could potentially result in the execution of arbitrary code or privilege escalation. -
Debian Security Advisory 5726-1
Operating System: Debian ≈ Packet Storm Jul 8, 2024 | 15:12 pmDebian Linux Security Advisory 5726-1 - Two vulnerabilities were discovered in the GSS message token handling in krb5, the MIT implementation of Kerberos. An attacker can take advantage of these flaws to bypass integrity protections or cause a denial of[…]
Read more... -
Debian: DSA-5726-1: krb5 Security Advisory Updates
Stay Vigilant with Timely Linux Security Advisories Jul 5, 2024 | 21:18 pm
Read more... Two vulnerabilities were discovered in the GSS message token handling in krb5, the MIT implementation of Kerberos. An attacker can take advantage of these flaws to bypass integrity protections or cause a denial of service.
Two vulnerabilities were discovered in the GSS message token handling in krb5, the MIT implementation of Kerberos. An attacker can take advantage of these flaws to bypass integrity protections or cause a denial of service. -
Debian Security Advisory 5725-1
Operating System: Debian ≈ Packet Storm Jul 4, 2024 | 15:32 pmDebian Linux Security Advisory 5725-1 - Johannes Kuhn discovered that messages and channel names are not properly escaped in the modtcl module in ZNC, a IRC bouncer, which could result in remote code execution via specially crafted messages.
Read more... -
Debian: DSA-5725-1: znc Security Advisory Updates
Stay Vigilant with Timely Linux Security Advisories Jul 3, 2024 | 20:35 pm
Read more... Johannes Kuhn discovered that messages and channel names are not properly escaped in the modtcl module in ZNC, a IRC bouncer, which could result in remote code execution via specially crafted messages.
Johannes Kuhn discovered that messages and channel names are not properly escaped in the modtcl module in ZNC, a IRC bouncer, which could result in remote code execution via specially crafted messages. -
Debian Security Advisory 5724-1
Operating System: Debian ≈ Packet Storm Jul 1, 2024 | 15:08 pmDebian Linux Security Advisory 5724-1 - The Qualys Threat Research Unit (TRU) discovered that OpenSSH, an implementation of the SSH protocol suite, is prone to a signal handler race condition. If a client does not authenticate within LoginGraceTime seconds (120[…]
Read more...
-
Ubuntu Security Notice USN-6913-1
Operating System: Ubuntu ≈ Packet Storm Jul 25, 2024 | 13:25 pmUbuntu Security Notice 6913-1 - Filip Hejsek discovered that phpCAS was using HTTP headers to determine the service URL used to validate tickets. A remote attacker could possibly use this issue to gain access to a victim's account on a[…]
Read more... -
Ubuntu Security Notice USN-6914-1
Operating System: Ubuntu ≈ Packet Storm Jul 25, 2024 | 13:25 pmUbuntu Security Notice 6914-1 - Filip Hejsek discovered that the phpCAS library included in OCS Inventory was using HTTP headers to determine the service URL used to validate tickets. A remote attacker could possibly use this issue to gain access[…]
Read more... -
Ubuntu Security Notice USN-6915-1
Operating System: Ubuntu ≈ Packet Storm Jul 25, 2024 | 13:24 pmUbuntu Security Notice 6915-1 - It was discovered that poppler incorrectly handled certain malformed PDF. An attacker could possibly use this issue to cause a denial of service.
Read more... -
Ubuntu Security Notice USN-6912-1
Operating System: Ubuntu ≈ Packet Storm Jul 24, 2024 | 13:40 pmUbuntu Security Notice 6912-1 - James Henstridge discovered that provd incorrectly handled environment variables. A local attacker could possibly use this issue to run arbitrary programs and escalate privileges.
Read more... -
Ubuntu Security Notice USN-6906-1
Operating System: Ubuntu ≈ Packet Storm Jul 24, 2024 | 13:37 pmUbuntu Security Notice 6906-1 - It was discovered that python-zipp did not properly handle the zip files with malformed names. An attacker could possibly use this issue to cause a denial of service.
Read more... -
Ubuntu Security Notice USN-6530-2
Operating System: Ubuntu ≈ Packet Storm Jul 24, 2024 | 13:35 pmUbuntu Security Notice 6530-2 - Seth Manesse and Paul Plasil discovered that HAProxy incorrectly handled URI components containing the hash character. A remote attacker could possibly use this issue to obtain sensitive information, or to bypass certain path_end rules.
Read more... -
Ubuntu Security Notice USN-6910-1
Operating System: Ubuntu ≈ Packet Storm Jul 24, 2024 | 13:35 pmUbuntu Security Notice 6910-1 - Chess Hazlett discovered that Apache ActiveMQ incorrectly handled certain commands. A remote attacker could possibly use this issue to terminate the program, resulting in a denial of service. This issue only affected Ubuntu 16.04 LTS.[…]
Read more... -
Ubuntu Security Notice USN-6907-1
Operating System: Ubuntu ≈ Packet Storm Jul 24, 2024 | 13:34 pmUbuntu Security Notice 6907-1 - Joshua Rogers discovered that Squid did not properly handle multi-byte characters during Edge Side Includes processing. A remote attacker could possibly use this issue to cause a memory corruption error, leading to a denial of[…]
Read more... -
Ubuntu Security Notice USN-6911-1
Operating System: Ubuntu ≈ Packet Storm Jul 24, 2024 | 13:33 pmUbuntu Security Notice 6911-1 - Arnaud Morin discovered that Nova incorrectly handled certain raw format images. An authenticated user could use this issue to access arbitrary files on the server, possibly exposing sensitive information.
Read more... -
Ubuntu Security Notice USN-6908-1
Operating System: Ubuntu ≈ Packet Storm Jul 24, 2024 | 13:32 pmUbuntu Security Notice 6908-1 - It was discovered that the Tomcat SSI printenv command echoed user provided data without escaping it. An attacker could possibly use this issue to perform an XSS attack. It was discovered that Tomcat incorrectly handled[…]
Read more...
-
Mailpit -- Content Security Policy XSS
FreeBSD VuXML Jul 26, 2024 | 00:00 am
Read more... -
Gitlab -- Vulnerabilities
FreeBSD VuXML Jul 25, 2024 | 00:00 am
Read more... -
electron29 -- multiple vulnerabilities
FreeBSD VuXML Jul 19, 2024 | 00:00 am
Read more...